January 22, 2026
January 22, 2026
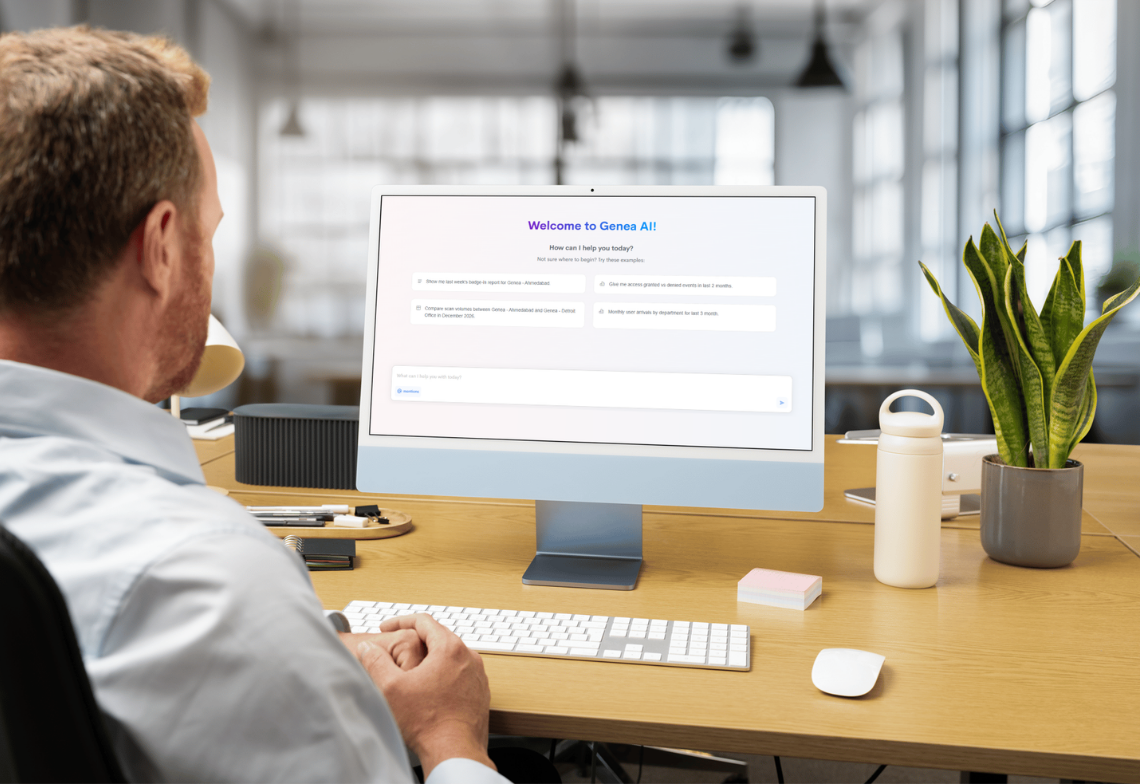
Genea