Disclaimer: We want people to be safe. We are able to do this by educating the public on security threats and possible vulnerabilities. Please do not use the following information on how to clone an rfid key card to exploit someone else’s security system or to try to gain access to unauthorized facilities.
One of the most commonly used technologies in the security industry is easier and cheaper to clone than you would ever imagine. I am talking about RFID key cards. Yes, the white card you were assigned when you started working in an office building. They look like this:
If you think that these cards are “safe” or “secure” or “impossible to hack,” you would be wrong. Very wrong. Because there are many different types of card technology today, we will refer to the vulnerable type of cards as “proximity cards.” So if someone wants to clone an rfid key card, it’s not actually hard thing to do.
Proximity cards use 125 kHz radio frequency fields to communicate when in close “proximity” to a reader, hence the name. So what exactly is a proximity card? Let’s take a look inside!
A prox card can basically be divided into three components: a coil, a capacitor, and an integrated circuit.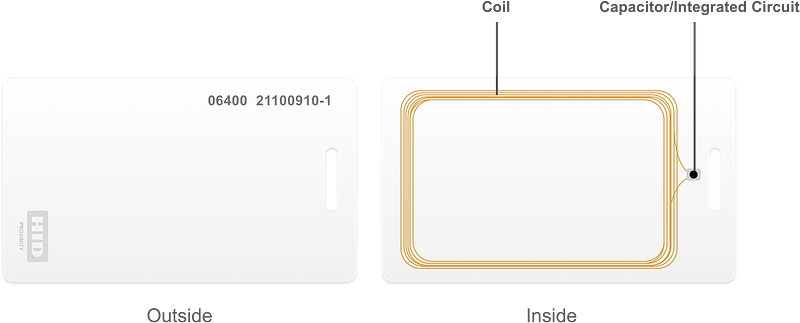
Nerd Alert! Skip if you simply just don’t care about the details. No hard feelings.
Cards use a simple LC circuit. When a card is presented to the reader, the reader’s electrical field excites a coil in the card. The coil charges a capacitor and, in turn, powers an integrated circuit. The integrated circuit outputs the card number to the coil which transmits it to the reader. The transmission of the card number happens in the clear — it is not encrypted.
With a basic understanding of radio technology and card formats, most office proximity cards can be hacked.
The hard coded card number that lives on the integrated circuit is the key here. Imagine that number is a name on a list for a party. When you walk up to the bouncer (the reader), he is going to check the list (the access control system) to make sure that your name appears before he let’s you in.
To hack most access control systems and gain unauthorized access, all you need to do is get this number.
Getting that key card number is actually much easier than it should be. There is an $11 device that you can buy on Ebay that can get the number for you.
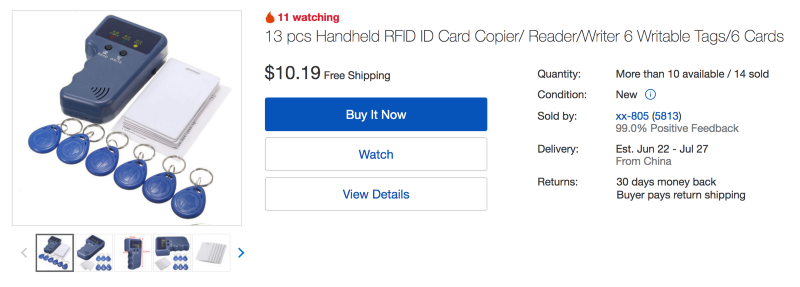
The RFID reader/writer can copy any 125 kHz proximity card that uses open 26 bit format. We estimate that nearly 70% of all prox cards are in this open, hackable format.
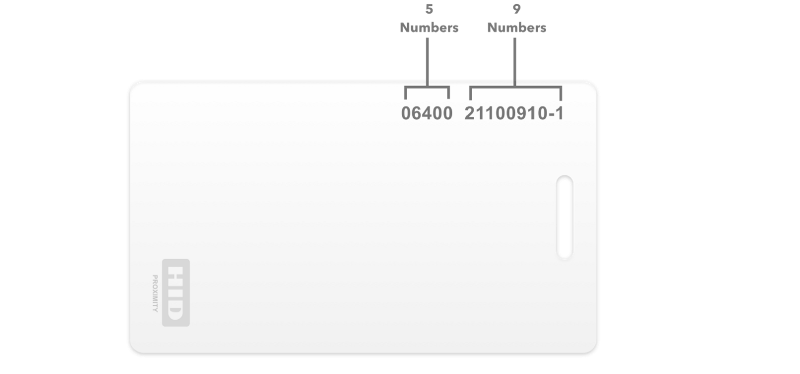
Before you go ahead and purchase the device for testing, refer to the layout of your key card. Look for a similar format to this:
How do I prevent this?
The true purpose of this post is to educate. Now that we know the vulnerabilities of the existing technology, let’s talk about how we can defend against threats.
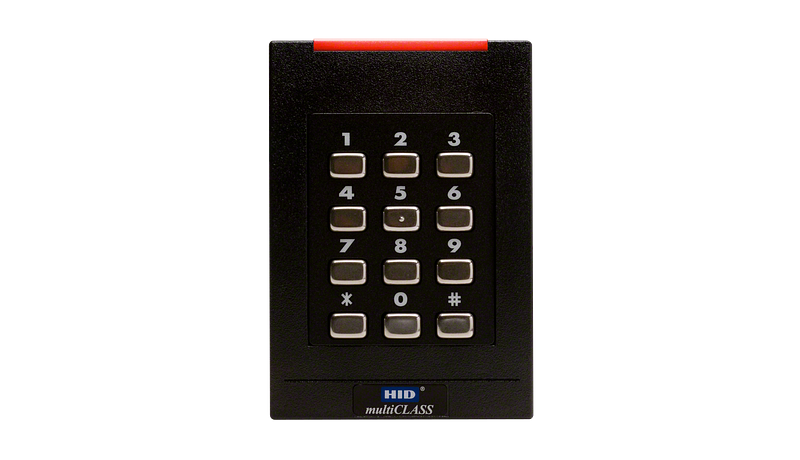
- Two-Factor Authentication — Key cards can be copied. They are easily lost or stolen, and we definitely do not have any problem sharing them. One precaution we can take is to require a second form of identification. Many access control systems will couple an access card with either ‘something you know’ or ‘something you are.’ ‘Something you know’ can be a password or a pin code. Pin Code readers, such as the one below, are often used in the physical access control world.
2. Contactless Smart Card Technology—As opposed to the 125 kHz, smart cards use 13.56-MHz. Its embedded integrated circuits can store and sometimes process data and communicate with a terminal via radio waves. Unlike proximity cards, the communication between the card and the reader is encrypted and secure. We use the amazing SEOS technology. These cards can also be used to exchange data and are great for logical access control.
3. Mobile Access—This option is our favorite. Smartphones are rapidly replacing access cards in the security industry. We are at the forefront of this movement. Mobile cards are easy to assign, monitor, and revoke in real time. They can not be copied or duplicated. And let’s face it, are you more likely to share your key card for the day or your phone? From a security and convenience standpoint, mobile access is second to none.
Interested in truly securing your office? Schedule a demo today and join the forward thinkers of the world!






